Security at Arduino
At Arduino, we embrace Security as an integral part of the development lifecycle in order to provide secure hardware, software and digital services to our customers.
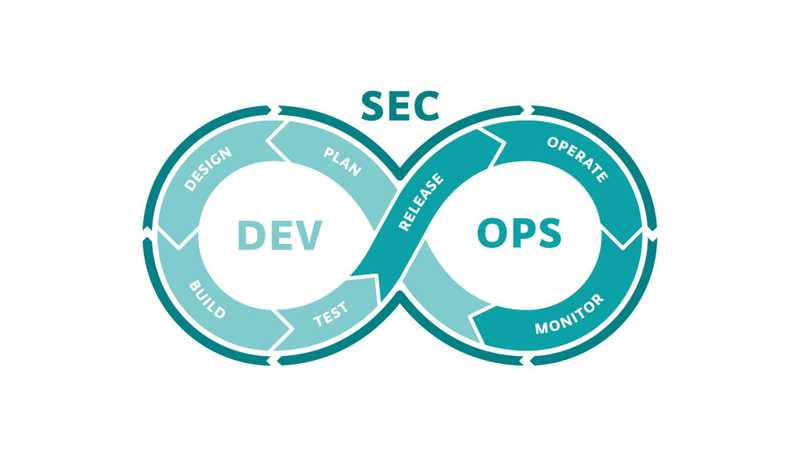
We follow a DevSecOps approach with focus on Security throughout each of the following phases:
- PLAN: security requirements are identified and analyzed. This involves assessing security risks and threats and determining the necessary security controls and measures.
- DESIGN: security requirements are considered while defining the product architecture. Any workflow needing special security attention is designed and reviewed in detail before implementation.
- BUILD: secure coding principles and best practices are followed to minimize vulnerabilities.
- TEST: automated security testing tools, such as static application security testing (SAST) are employed to scan source code and identify potential security flaws. Secure Component Analysis is also performed to ensure that external components do not compromise the security of our software. CI/CD pipelines are configured to perform these security tests as part of the build and test processes. Security vulnerabilities are identified and classified according to their priority and risk, so that any critical issue can be fixed before moving to the next phase.
- RELEASE: security best practices are employed to ensure that the deployment environment is secure. This involves applying secure configurations, managing access controls, and implementing secure network architectures.
- OPERATE: regular security audits and penetration tests are conducted to assess the system's resilience to attacks and ensure compliance with security best practices.
- MONITOR: monitoring tools are used to provide visibility into the Cloud services status, and detect anomalous behaviors and potential threats. In the event of a security incident or breach, Security Engineers collaborate with development and operations teams to address the incident, mitigate the impact, and restore the system's security and functionality.
Throughout each of these phases, Security is not viewed as a separate function but rather as an integrated responsibility of all teams involved in the software development and operations process, inspired by a Shift-Left security approach. Security Engineers work alongside developers and operations personnel to provide guidance, conduct security assessments, and ensure that security controls are effectively implemented at each stage.
The following articles detail how security principles are applied in different areas of our products and digital services.